From Understanding to Anticipation: The Purpose of Threat Modeling
The primary goal of Threat Modeling is to anticipate and mitigate attack vectors, vulnerabilities, and threats before they can be exploited. This structured approach aligns closely with federal guidance, including NIST SP 800-30 “Guide for Conducting Risk Assessments” and NIST SP 800-154 “Guide to Data-Centric Threat Modeling.” By understanding how adversaries may target a system, organizations gain the insight needed to strengthen their defenses proactively rather than reactively.
Threat Modeling provides a clear methodology for examining how systems operate, how data flows, where weaknesses exist, and how attackers may attempt to compromise them. In a world of rapidly changing architectures, APIs, cloud services, and third-party integrations, this discipline has become essential.
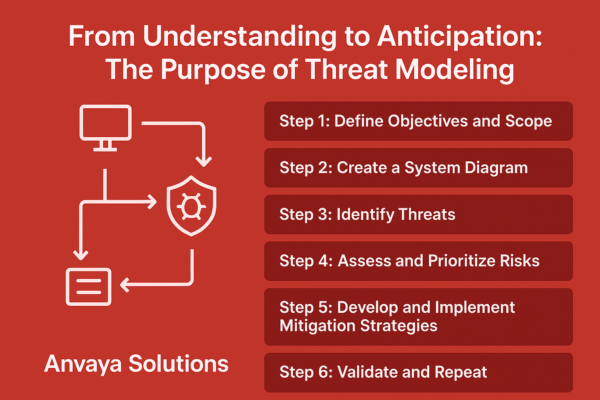
At a high level, effective Threat Modeling follows six core steps.
The Six Key Steps of Threat Modeling
Step 1: Define Objectives and Scope
The first step in building a threat model is to clearly define the objectives of the exercise and the scope of the system or application being analyzed. The system is then categorized using FIPS199, focusing on the data that is served by the application and develops an understanding of the business goals. By outlining what needs to be protected and why, the Anvaya team can prioritize efforts based on the impact. The purpose of threat modeling is to think like an attacker and identifying all potential attack paths
Step 2: Create a System Diagram
The system/application is “decomposed” by creating a detailed system diagram highlighting the boundaries and integrations to external systems. This helps visualize the interaction of the components (both internal and external) and identify the potential vulnerabilities. This crucial step maps the data flows, helps identify the entry/exit points, and the trust boundaries. This is based on the philosophy of “you can’t protect what you don’t know”.
Step 3: Identify Threats
Using threat modeling frameworks such as STRIDE or PASTA, Anvaya will systematically identify potential threats to the system and use the MITRE ATT&CK framework to map potential threats to specific adversary tactics and techniques (TTPs) Possible attacker behaviors, attack vectors, vulnerabilities, and techniques to exploit are discussed in this step.
Step 4: Assess and Prioritize Risks
The next step is the prioritization based on the impact and likelihood. To do this, the Anvaya team will use the Common Vulnerability Scoring System (CVSS), to prioritize risks based on their severity.
Step 5: Develop and Implement Mitigation Strategies
After prioritizing risks, the Anvaya team will recommend mitigation strategies to address the threats. This may include implementation of additional security controls, changes in architecture/design, and updating policies and procedures. Mitigation strategies will be tailored to specific threats and aligned with organizational mission, goals, and available technology and resources.
Step 6: Validate and Repeat
Threat modeling is a cyclical process that will be repeated. After implementing mitigations, the Anvaya team will validate the efficacy through tests based on the specific TTPs identified in the MITRE ATT&CK analysis. The threat modeling exercise will be revisited to account for system changes, emerging threats and techniques. This ensures the efficacy and relevance of the model.
Why Threat Modeling Matters
Threat Modeling enables organizations to move beyond reactive security. It provides structure, visibility, and foresight — empowering teams to address weaknesses long before adversaries discover them. This approach strengthens architectures, supports compliance requirements, and builds enduring resilience.
- Proactive risk mitigation: Address threats before exploitation occurs.
- Data-centric security: Align protections with the sensitivity and value of the data.
- Improved architecture: Build secure-by-design systems with clear trust boundaries.
- Better prioritization: Focus on risks that have the highest impact and likelihood.
- Continuous assurance: Adapt as systems and threats evolve.
Why Partner with Anvaya Solutions
As highlighted on our website: “Anvaya Solutions brings together experienced consultants, proven methodologies, and leading technologies to improve your security maturity and resilience.”
Our team brings deep expertise in Threat Modeling, NIST-aligned assessments, risk management, and adversary-aligned testing. Whether supporting public or private sector environments, Anvaya helps organizations build repeatable, scalable Threat Modeling programs that strengthen security and reduce real-world exposure. The purpose of threat modeling is to build a more secure environment for our partners.
Strengthen Your Security Posture Today
Threats evolve constantly — your defenses should too. With Anvaya Solutions’ Threat Modeling services, you gain the visibility, structure, and proactive insight needed to stay ahead of emerging risks.
Secure. Protect. Thrive!