How to Secure Your Application in 2026
How to Secure Your Application in 2026 Modern businesses rely more and more on software every day. Even then, more and more companies are asking the same critical question: How do you truly secure your application? Application Security in 2026 Requires a Shift in Thinking Entire businesses now run on software, and the security of […]
Read MoreHow to Choose the Right Penetration Test Partner
Beyond the Scan: How to Choose the Right Penetration Testing Partner Everyone needs to know how to chose the right penetration test partner. Engaging an independent Vulnerability Assessment (VA) and Penetration Testing (PT) consultant is a strategic decision that directly impacts an organization’s security posture. Drawing from real-world practitioner experience, this blog breaks down what […]
Read MoreCloud Security Lifecycle Best Practices by Anvaya
Cloud security lifecycle best practices and Anvaya’s practical take on protecting what changes every day Cloud security matters because the cloud changes faster than most security programs can keep up with. The cloud is a living environment made of identity, APIs, automation, managed services, short-lived workloads, third-party integrations, and constant deployments. That velocity is exactly […]
Read MoreThe Purpose of Threat Modeling
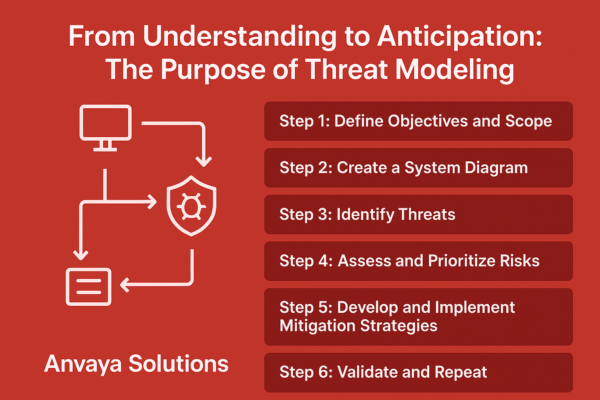
From Understanding to Anticipation: The Purpose of Threat Modeling The primary goal of Threat Modeling is to anticipate and mitigate attack vectors, vulnerabilities, and threats before they can be exploited. This structured approach aligns closely with federal guidance, including NIST SP 800-30 “Guide for Conducting Risk Assessments” and NIST SP 800-154 “Guide to Data-Centric Threat […]
Read MoreAttack Surface Management vs. Vulnerability Management: Why Continuous Visibility Wins
From Periodic Scanning to Continuous Visibility For years, organizations relied on traditional vulnerability management (VM) — scanning known assets, identifying weaknesses, and patching them. While VM remains essential, today’s cloud-driven, interconnected environments have dramatically changed the security landscape. Modern enterprises aren’t defending static networks anymore. They’re managing dynamic, constantly shifting attack surfaces made up of […]
Read MoreCMMC – Protecting the Future of Your DoD Contracts Starts Now
Why CMMC Matters to You If your organization is part of the Defense Industrial Base (DIB), cybersecurity is no longer just a best practice – it’s going to be a contractual requirement. The Cybersecurity Maturity Model Certification (CMMC) ensures that every company handling Federal Contract Information (FCI) or Controlled Unclassified Information (CUI) meets strict data […]
Read More90% of the World’s Data Was Created in Two Years!
Why Penentration Testing is More Critical Than Ever 90% of data, in existence today, was created between 2021 – 2023. This explosion of data creation underpins deep shifts in how we live, work, and interact with technology. But with that volume of data come equally complex issues regarding its security. The Data Deluge: A Two-Edged […]
Read MoreCybersecurity Threats in 2025: Rising Costs and Real Solutions
The auction house, Christie’s, has fallen under a major ransomware attack. This attack took down
their main website just days before an auction that will feature over $840 million worth in works of
art.
The Story of the Christie’s Ransomware Attack Illustrates That Penetration Testing Is More Important Than Ever
The auction house, Christie’s, has fallen under a major ransomware attack. This attack took down
their main website just days before an auction that will feature over $840 million worth in works of
art.